Visitor Management + Access Control: The Perfect Duo
Visitor Management + Access Control: The Perfect Duo Walk into any modern workplace today, and you’ll
10 min reading time
Updated on May 05, 2026
Share this article
In the first blog, we discussed why Scypher, Spintly’s credential management platform, exists and the problems it solves at scale. This blog focuses on the next question enterprise leaders usually ask:
To answer that, we look inside Scypher’s architecture, its core components, and the path a credential follows from creation to enforcement.
Scypher is built on a simple but powerful idea:
Centralise credential management. Keep access enforcement local.
Traditional access control systems were designed in a world where credentials were physical cards. They work well when credentials are static and change infrequently. But modern enterprises operate very differently:
Managing this level of change using manual or semi-manual workflows creates operational and security gaps.
Scypher addresses this by modernizing how credentials are managed without disrupting how access is enforced.
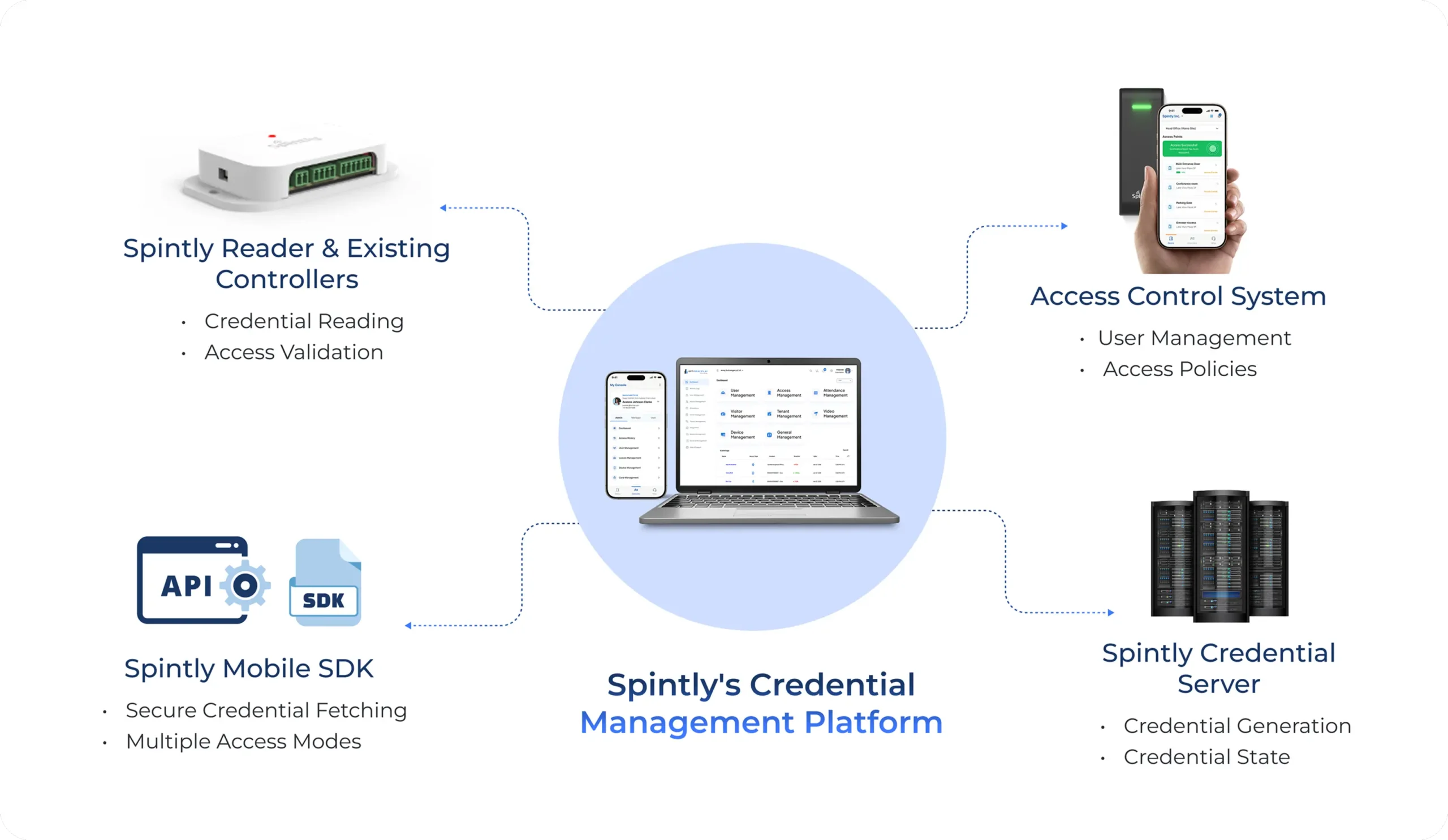
Spintly’s credential management platform is made up of four core components. Each component has a clearly defined responsibility, and together they form the complete system.
1. Access Control System (ACS)
The Access Control System remains the system of authority.
It continues to:
Scypher does not override or replace the ACS. Instead, it works alongside it. Whenever a credential is required, the ACS initiates the request and remains responsible for permission assignment.
2. Spintly Credential Server
The Spintly Credential Server is the cloud-based component of the platform.
Its role is to manage the credential lifecycle, which includes:
What the Credential Server deliberately does not do:
Think of it as the system that creates and manages credentials, not the system that enforces access.
3. Spintly Mobile SDK
The Spintly Mobile SDK is how credentials reach users’ phones.
Instead of requiring users to install a separate Spintly app:
The SDK handles:
From a user’s perspective, access feels like a native feature of the app they already use. From a system perspective, the SDK acts as a secure carrier for digital credentials.
4. Spintly Reader and Existing Controllers
At the physical access point, Scypher integrates into the existing infrastructure.
The reader’s responsibility is straightforward:
The controller:
In some deployments especially new buildings, the reader can also act as a controller. However, Scypher does not assume this model and works seamlessly with existing controllers.
To understand how these components work together, let’s walk through the credential issuance and access flow.
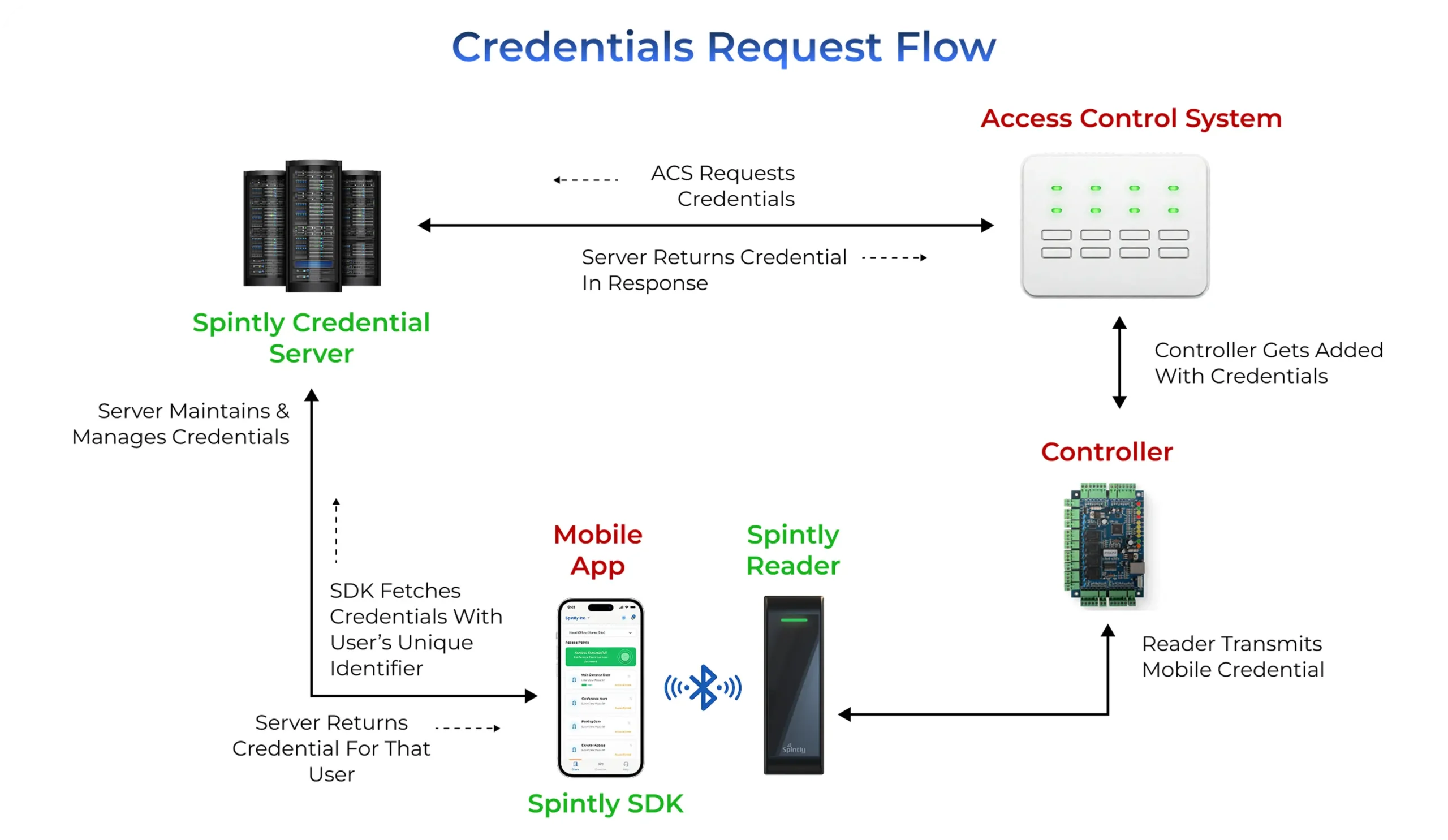
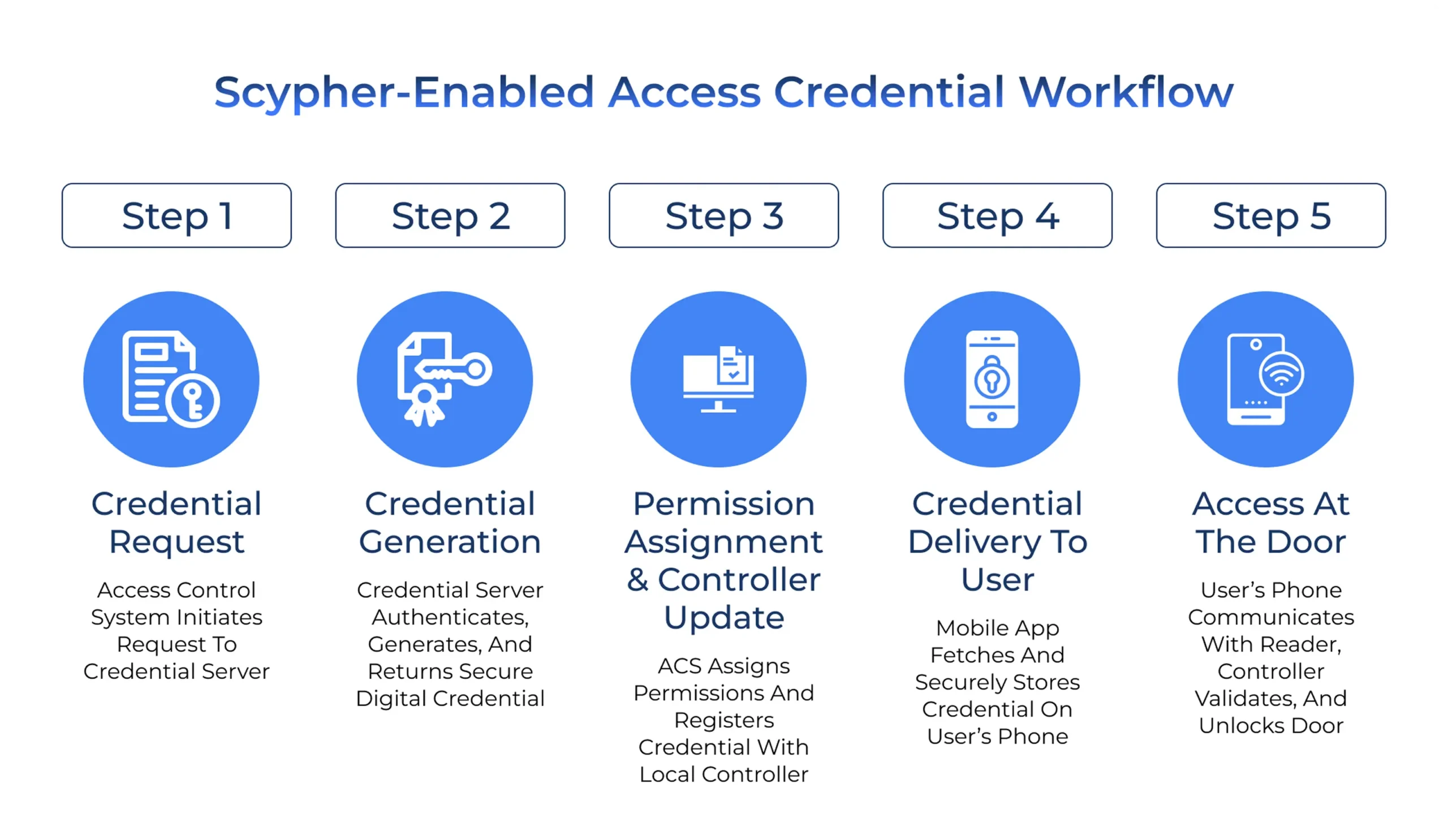
Step 1: Credential Request
When a user needs access:
At this stage, no access is granted. A credential is simply being requested.
Step 2: Credential Generation
The Credential Server:
The credential now exists, but it is not yet active at the door.
Step 3: Permission Assignment and Controller Update
Back in the ACS:
This step ensures that access enforcement remains local and reliable.
Step 4: Credential Delivery to the User
On the user side:
There is no physical card issuance, printing, or handover involved.
Step 5: Access at the Door
When the user approaches the door:
Scypher is not involved in this real-time decision. The controller always decides.
In short:
Revocation follows the same clear separation of responsibilities.
When access needs to be removed:
Even if:
Access will fail, because the controller no longer recognises the credential. This preserves the same security guarantees enterprises expect from traditional access control systems.
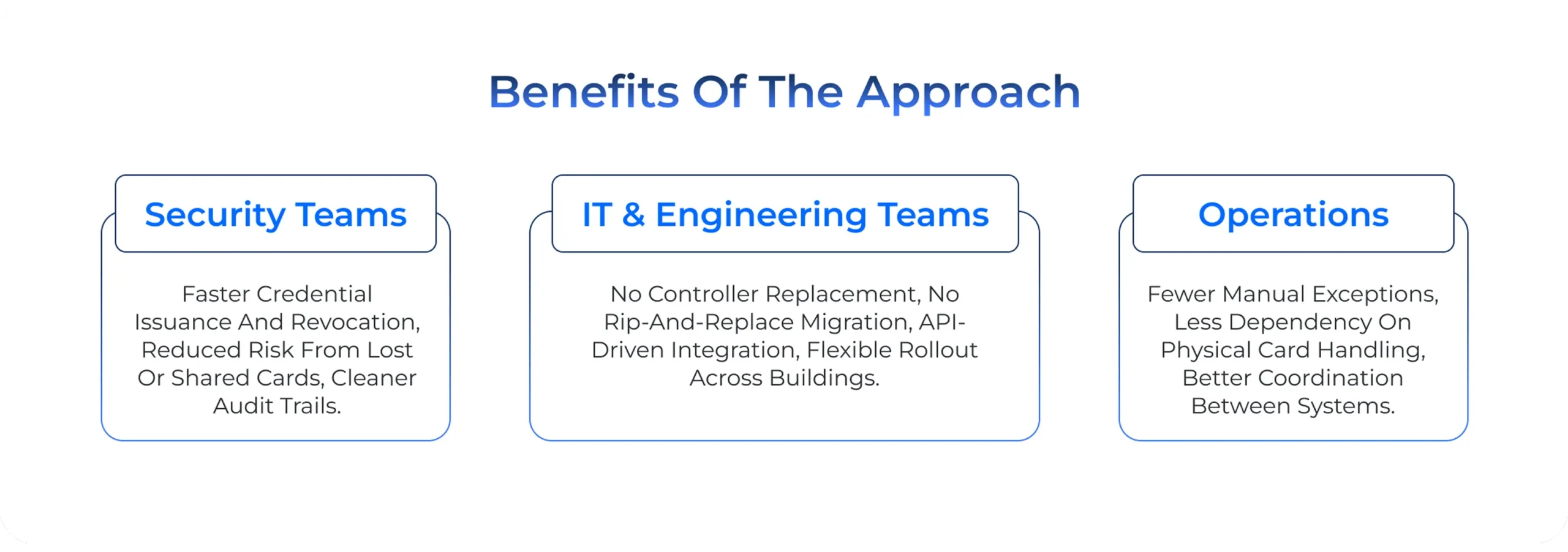
Spintly’s credential management platform works because it respects real-world enterprise constraints:
By separating credential management from access enforcement, Scypher allows enterprises to adopt mobile access and modern credential workflows without destabilising existing systems.
For security teams:
For IT and engineering teams:
For operations:
At its core, Scypher is built around a simple realization: access control doesn’t break at the door, it breaks in how credentials are managed over time.
As enterprises grow, people join, move roles, take on temporary access, and leave. When credentials are still handled through manual or fragmented workflows, even the most reliable access control systems start to feel harder to manage. Delays creep in. Exceptions become routine. Risk quietly increases.
Scypher was designed to solve this exact problem.
By separating credential lifecycle management from access enforcement, Scypher modernises how credentials are issued, delivered, and revoked without disturbing the controllers, wiring, and access logic that enterprises already trust. The door continues to behave the same way. The controller continues to make the final decision. What changes is everything behind the scenes.
The result is a system that scales naturally with the organization: faster onboarding, cleaner revocation, better visibility, reduced costs and fewer operational dependencies without forcing disruptive infrastructure changes.
In short, Scypher doesn’t ask enterprises to rethink access control. It simply makes credential management finally catch up to how modern organizations actually operate.
Visitor Management + Access Control: The Perfect Duo Walk into any modern workplace today, and you’ll
The Role of AI in Modern Access Control Systems Access control has always come down to
Introducing Scypher- Spintly’s Credential Management Platform for Digitising Access Control For decades, enterprise access control has
Inside Spintly’s Credential Management Platform- Architecture, Flow, and Core Benefits In the first blog, we discussed
Comparing Access Control Architectures: Wiegand vs OSDP vs BLE Mesh Access control systems rely on communication
Choosing the Right Access Control Integration Model – Why Cross-Team Validation Is Critical Choosing an access
Integrating Third-Party Apps with the Spintly SDK and APIs: A Developer’s Guide Many organizations today already
What is Aliro and how will it impact the Access control industry We use our phones
What are the current trends and innovations in MFA and access control? For a long time,
NFC vs BLE: Which Is Better for Access Control? Which Is Better for Access Control, NFC