For decades, enterprise access control has followed the same basic pattern.
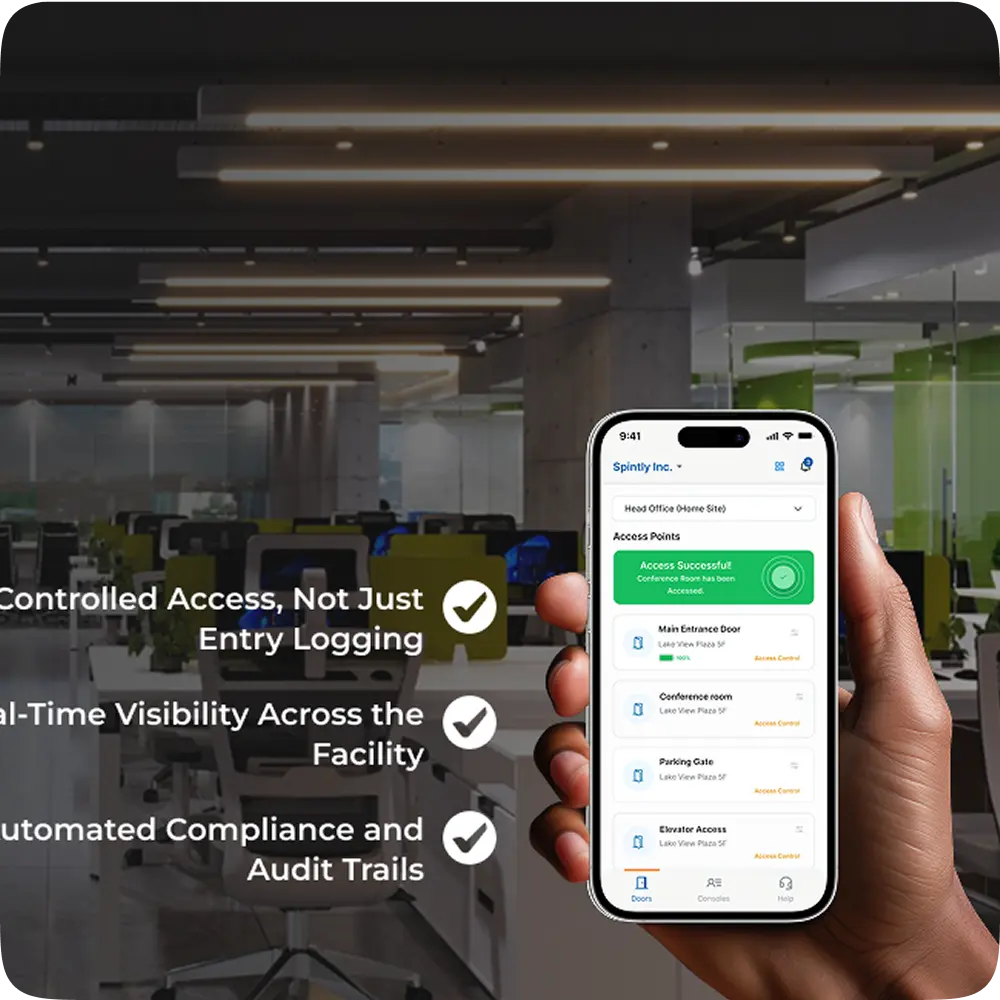
If you walk into most enterprise buildings today, the system looks modern on the surface. There are sleek readers at the door, controllers housed in panel rooms, and an admin console that has been running reliably for years. Doors open quickly, locks respond as expected, and from the outside, everything appears stable.
But behind the scenes, much of the workflow still reflects an earlier era.
When someone joins the organization, a physical card needs to be issued. That card is manually added to the system, permissions are configured, and the card is handed over. The same process repeats for contractors, visitors, tenants, and temporary staff often across multiple buildings and locations.
At a small scale, this approach works.
At enterprise scale, it introduces operational overhead and security risk.
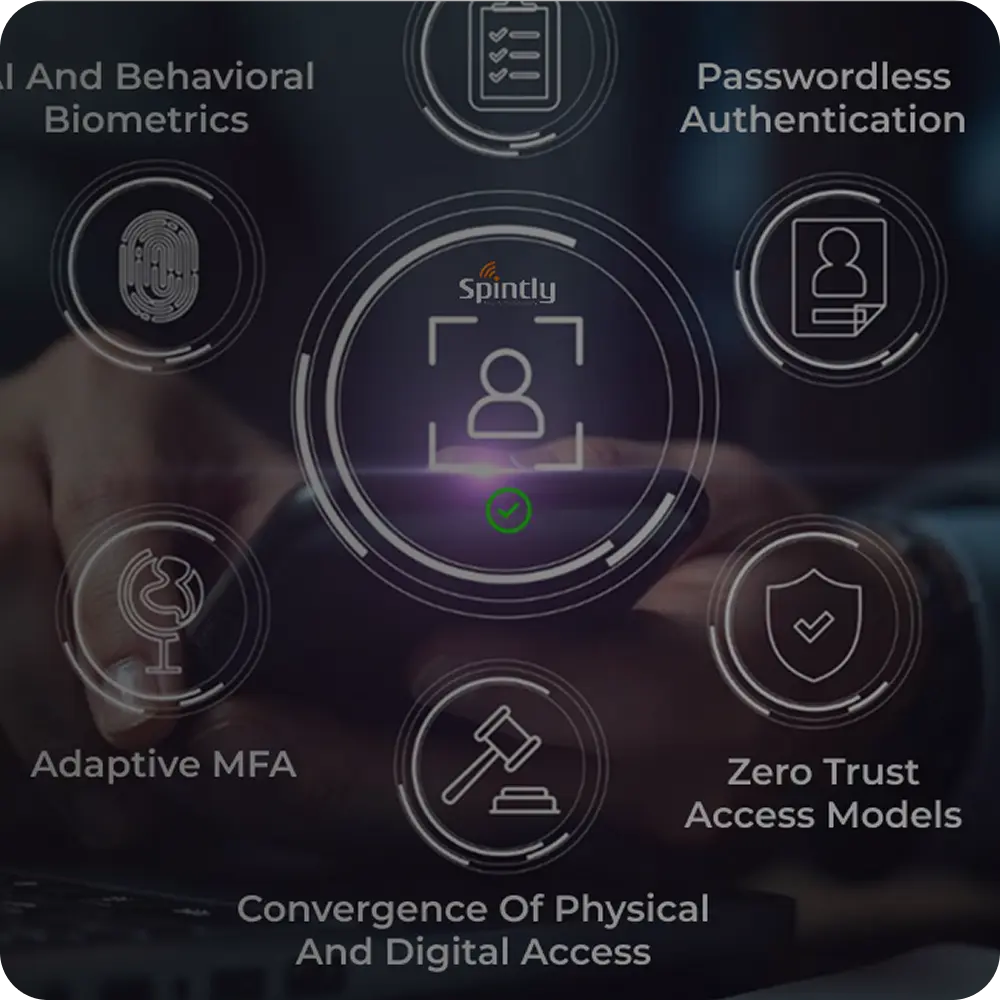
The issue isn’t door performance or system uptime. It’s how credentials are issued, managed, and revoked consistently over time. As organizations grow, the number of users, systems, and access scenarios increases faster than traditional credential workflows were designed to handle. This creates gaps in visibility, control, response and costs in the long run.
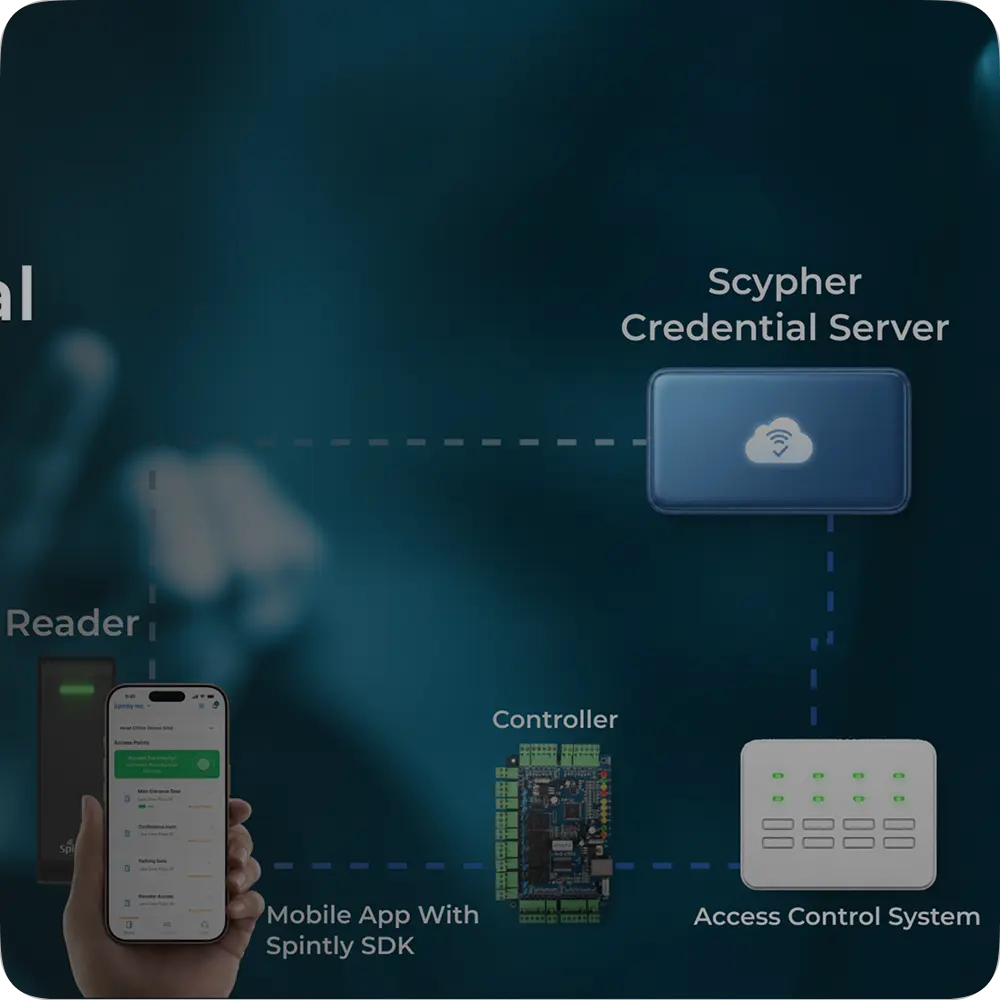
That’s the gap Scypher is built to address.