Access control has always come down to a basic decision. Who gets in, and who does not.
For a long time, that decision relied on fixed credentials like keys, cards, or PINs. If the input matched, access was granted. If it did not, the door stayed shut. Simple, reliable, but built for a much more predictable world.
That world has changed.
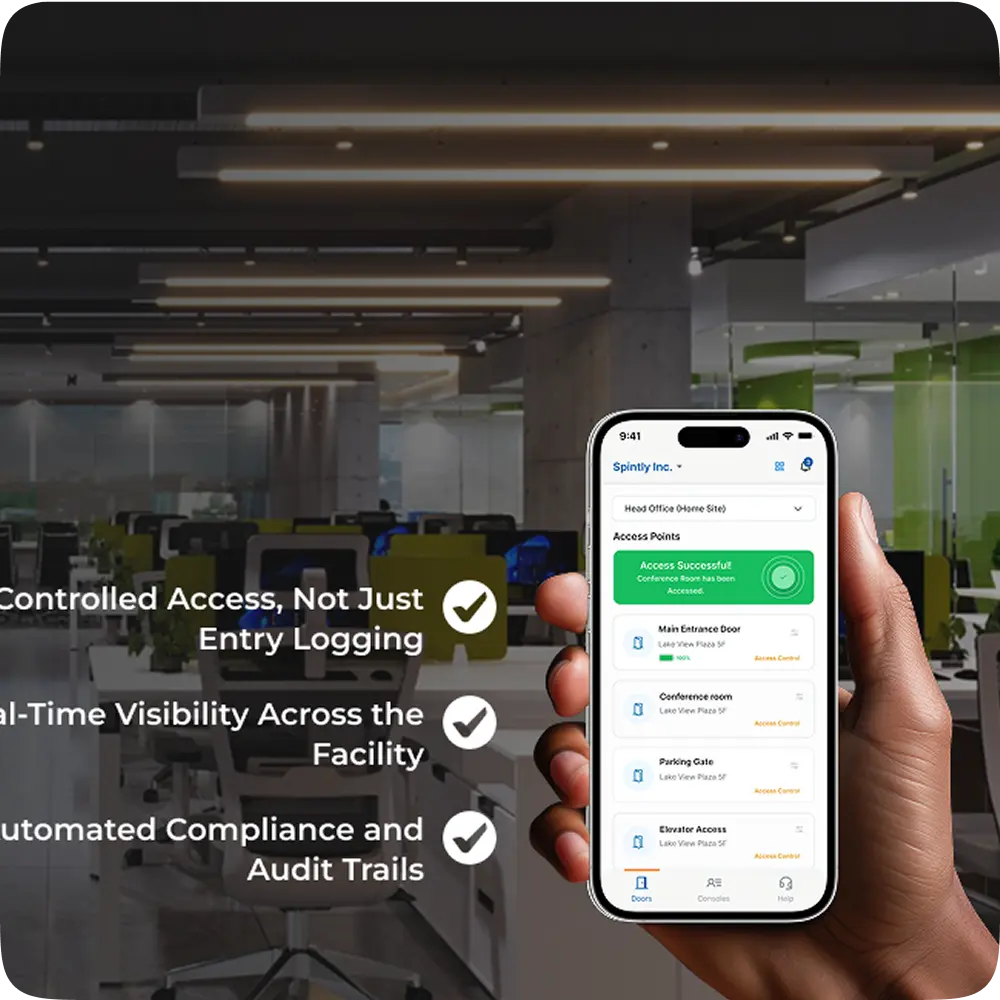
Workplaces today are fluid. Teams are hybrid, offices are shared, and there is a constant flow of visitors, vendors, and external partners. At the same time, security risks have become less obvious and more nuanced. Static systems struggle to keep up with this kind of environment.
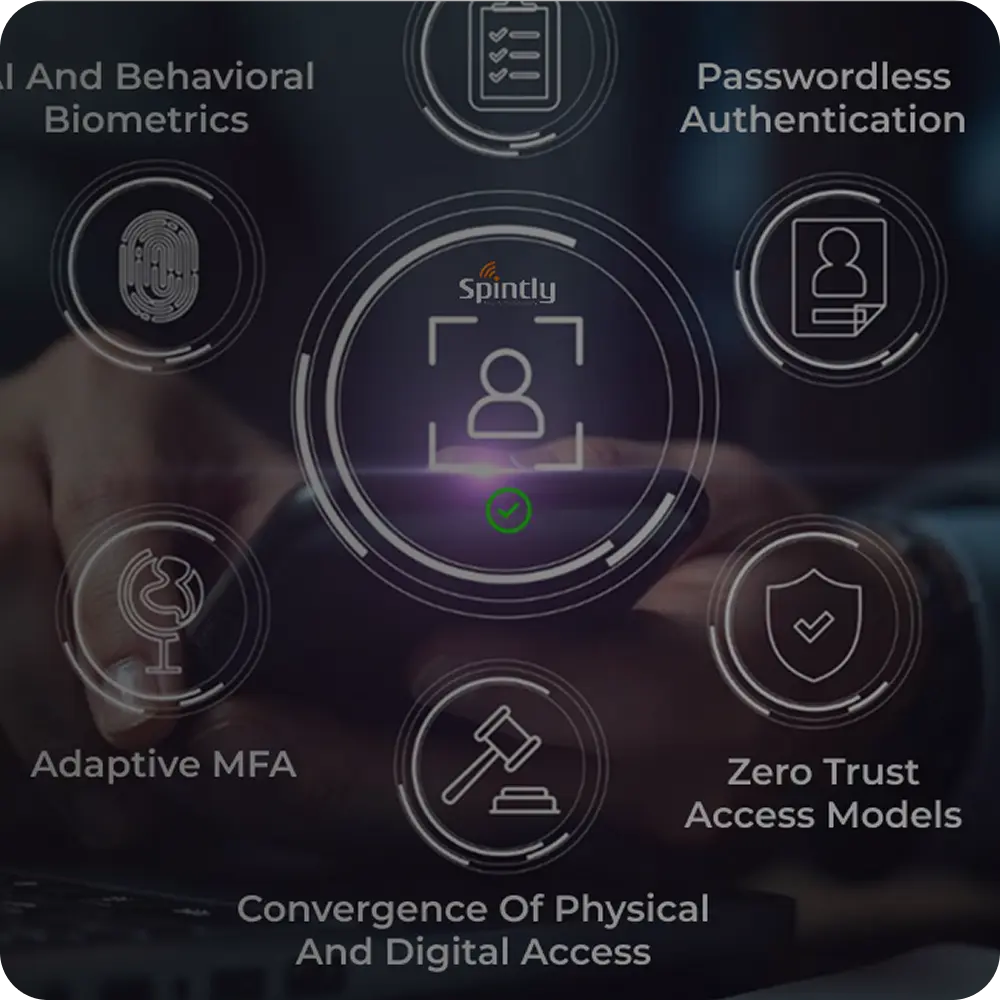
This is where AI starts to make a real difference.