Face Recognition

Spintly Face Recognition system brings smart face identification and authorization to the Spintly ecosystem.
Technological Breakthroughs that have the Potential to Reshape Modern Access Control

Technological breakthroughs that have the potential to reshape modern access control “When something is important enough, you do it even if the odds aren’t in your favour.” -Elon Musk This is the life mantra of Mr. Rohin Parkar, Co-Founder and CEO, Spintly, who has a background in wireless technology and engineering, has always aspired to […]
Why are Organizations Opting for Contactless VMS?

WHY ARE ORGANIZATIONS OPTING FOR CONTACTLESS VISITOR MANAGEMENT SYSTEMS? Businesses must adjust to swings in people’s capacity and willingness to follow standards for the sake of the public, in addition to following specific regulations and each organization implementing its own safety protocol Since the year 2020, we have had a better understanding of the Coronavirus […]
BIOMETRICS – The Future and recent trends in access control

BIOMETRICS – The Future and Recent Trends in Access Control Biometric Security Systems Explained What is the purpose of biometrics in access control? To begin with the history, the term biometric is derived from the Greek vocabulary, where Bio means Life and Metric means To Measure. In simple words, the biometric access control means a […]
Why does Contactless Technology play a major role?
Why does Contactless Technology play a major role? In today’s digital world, an increasing number of SMEs and start-ups are automating their routine day-to-day tasks. While most organizations now use card readers, biometric devices, and other digital devices, they still rely on manual time tracking and complex spreadsheets to track employees’ time and attendance. Manual […]
Webinar on Technology and related Solution of Wireless Access Control

Webinar on Advantages of Wireless Access Control Spintly is transforming the physical security industry with its fully wireless, cloud-based access control system. It removes the complexity out of the process of deploying an access control solution in a building. With absolutely no wiring the installers can save more than 60% of their time and cost and […]
Recent trends & future of Access Control in the post COVID era

Recent Trends & Future of Access Control in the post COVID Era 2020 was a challenging year marked by global tumult with the onset of the COVID-19 pandemic. This unprecedented and widespread healthcare system crisis has changed the lives of people worldwide. This disruption has not only given rise to the new norm of mask […]
Smart Access Control for the Hospitality industry

Smart Access Control for the Hospitality Industry Welcome to the next level of Smart Access Control in the Hospitality industry The hospitality industry is just not confined to hotels, tourism, restaurants and bars; but it’s an Experience, which remains on the “best memorable moments” page in people’s life. Managing a hotel, controlling its staff, protecting […]
Webinar on Advantages of Wireless Access Control

Webinar on Advantages of Wireless Access Control Making the switch from traditional Access facility to Wireless access control is easier than you think. It also quickly repays your investment with simpler, more flexible and efficient security management.During the introduction to the Advantages of Wireless Access Control webinar, Spintly CEO and Co-Founder Rohin Parkar will provide […]
Multi-Factor Authentication in Access Control
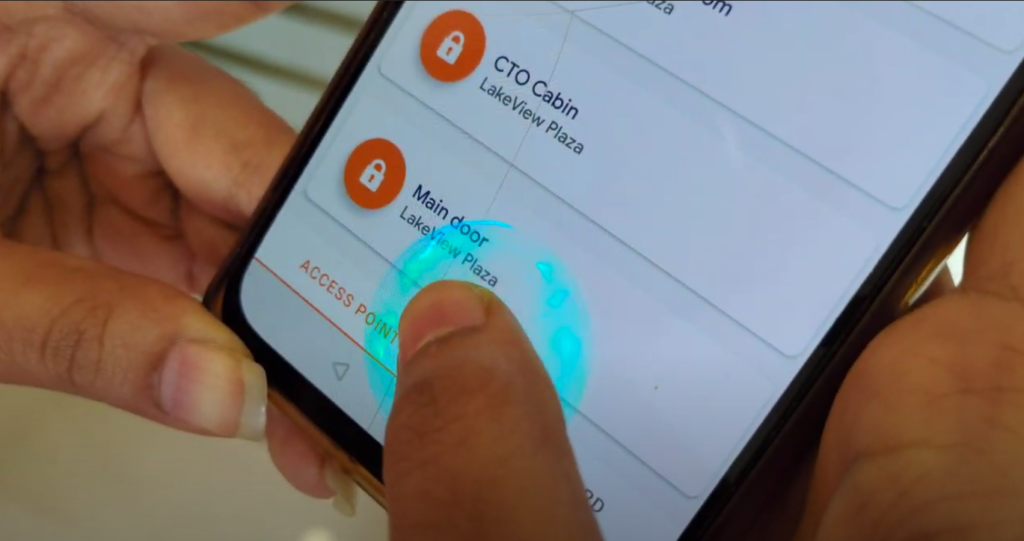
Multi-Factor Authentication in Access Control What is Multi-Factor Authentication (MFA)? Multi-factor Authentication refers to security technology that requires more than one verification method to verify a user’s identity to gain access to an application, online account, or any asset like a door. Most often a two-factor authentication method is used. Why is it necessary? We […]